
Google’s famed autocorrection feature is made simple with APILayer’s relevant API.
Google is without a doubt, the most widely used web engine in the world. We all use Google to have a solution for our every problem. But have you ever thought about why Google is so commonly used? While there are many other search engines like Yahoo, Bing, etc.
The thing about Google’s fame is that it makes everything so easy for you. You type one word in the search bar and you get dozens of related suggestions in a few seconds. And one of the great features of Google is the “Did you Mean” functionality.
What is the “Did You Mean” Algorithm?
We all use search engines and to be very fair, some of us are very bad at spelling or sometimes we don’t exactly know what we want so we just write something. In response, Google still brings the results to our query with a prompt saying Did you Mean This?
Let’s see an example of how this feature works. If you search the below line:
“did yuo maen ths”
Google will automatically return the results for
“did you mean this”
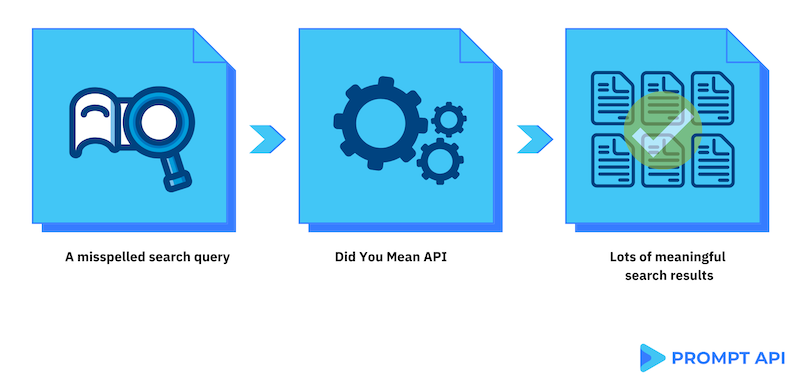
So, this feature is a combination of autocorrect and word prediction. And now you can use these methods to create your own Did You Mean feature. Thanks to our Did you Mean This API.
How does Did you Mean This Algorithm Work?
We have provided an API that you can easily embed in any of your applications. This API can be used for multiple purposes like
- autocorrect words,
- spelling mistakes,
- correcting grammatical errors, etc.
When you make a search, machine learning algorithms process you’re query and understand if there are not any (or a few) search results for it, but there is a similar word with lots of search results. Then it makes a decision to provide more meaningful results.
Some Examples For Did You Mean Algorithm
● If you have an eCommerce store, Did you Mean This feature can be a great asset for you. This can save a lot of your revenue. You must be wondering how this feature can help you in your business.
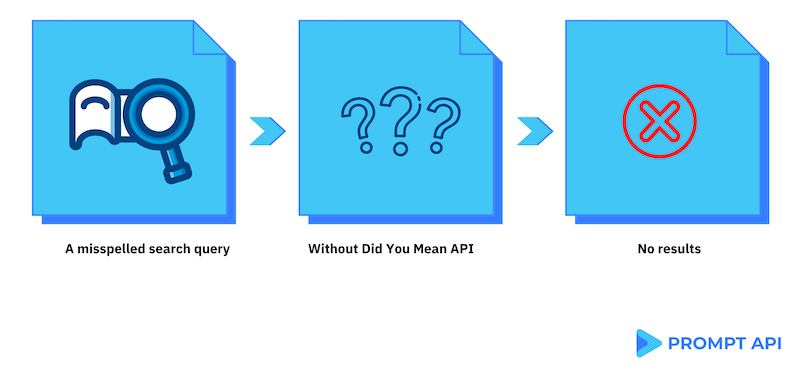
Imagine a case where a user comes to your website and searches for a thing but with the wrong spelling, in a normal case, the system would return that no results found for your query.
Let’s see an example, the user enters a query ”vakum cleaner”. In normal cases, the website would return that ‘no results’ found. But if you are using our Did you Mean This API, then it would automatically predict what the user is trying to find and would return the results for ”vacuum cleaner”. This will make the visitors stay on your website and they might purchase more items from your website.
● You have developed an App that has a feature of online chatting or interacting with other users. Users generally don’t care about spellings these days and most of the words are written with the wrong spelling and wrong grammar. Some keyboard apps provide autocorrect functionality and identify spelling mistakes. But it does not work as much as we want.
You can add this functionality to your APP easily by using our Did you Mean This API. This will provide a better user experience for your app users. They get the right results even if they did not write it correctly.
For example when a user writes this sentence in the app:
“tomoto suop recipe”
This sentence is corrected by the API endpoints as follows:
‘tomato soup recipe”
Now if you want to create your own Did You Mean feature please check out our Did You Mean This API page which also has great documentation support.
